Element – 3.4 (Risk Assessment)
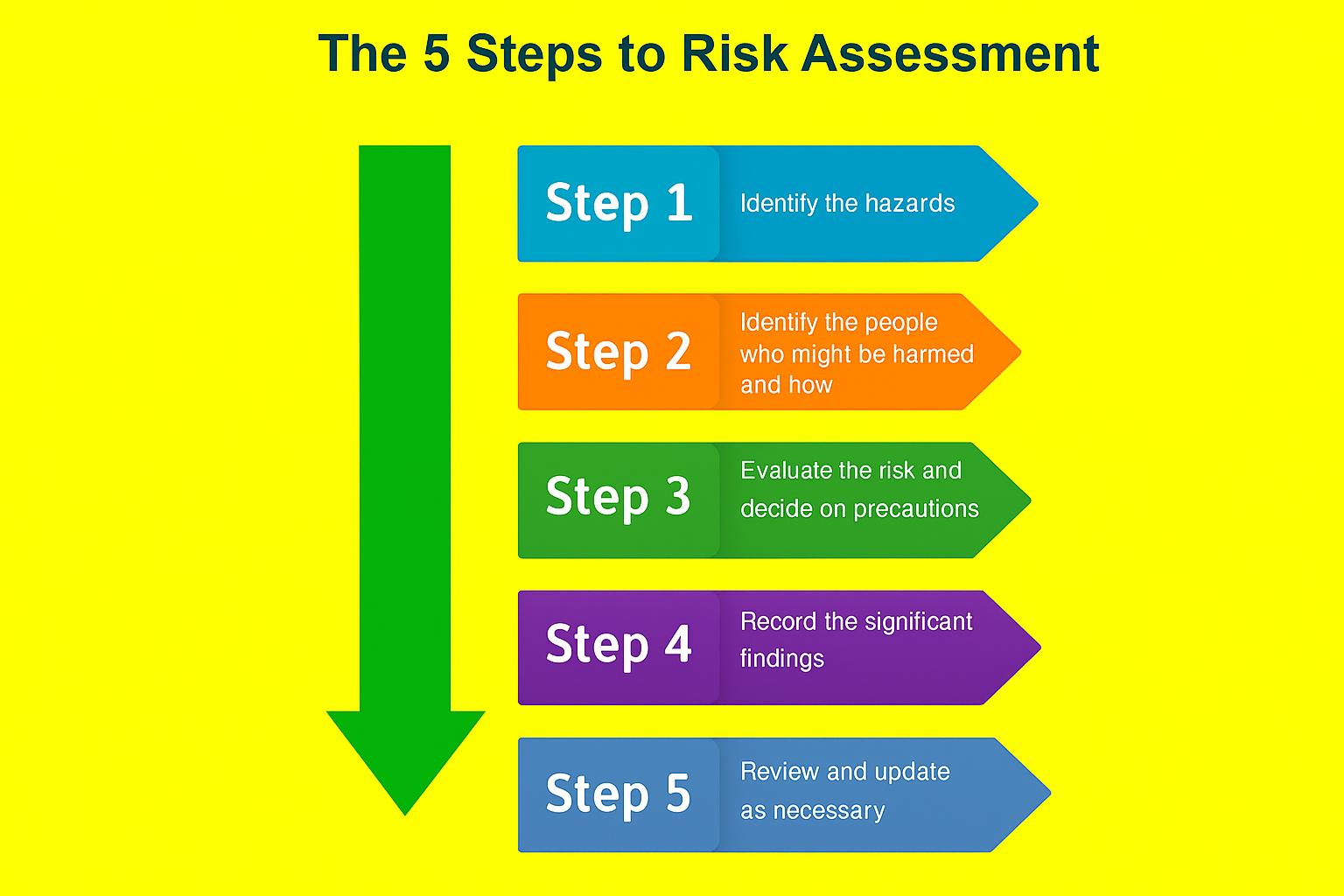
The Five Steps of Risk Assessment
As defined by hse :-
Key Words and Phrases
Risk Profiling:
The process of identifying and assessing the range of risks that threaten an organisation along with recognition of their likelihood and probable impacts, the current risk management controls in place and the identification and prioritisation of further control measures.
Key Words and Phrases
Risk Profiling:
The process of identifying and assessing the range of risks that threaten an organisation along with recognition of their likelihood and probable impacts, the current risk management controls in place and the identification and prioritisation of further control measures.
Key Words and Phrases
Risk Assessment:
The formal process of identifying preventive and protective measures by evaluating the risks arising from a hazards, taking into account the adequacy of any existing controls, and deciding whether or not the risk is acceptable.
Risk Profiling
Each organisation will have its own risk profile.
A risk profile examines:
- The nature and level of the threats faced by the organisation.
- The likelihood of those adverse effects occurring.
- The level of disruption and costs associated with each type of risk.
- The effectiveness of controls in place to manage those risks.
Risk Profiling
The outcome of risk profiling will be that the right risks have been identified and prioritised for action, the right control measure have been identified and implemented and minor risks have not been given a disproportionate priority.
Risk Profiling
The Risk Profiling Process:
- Identify the risk that threaten the organisation.
- Identify the health and safety impacts and the business impacts associated with each threat.
- Identify how well each threat is controlled.
- Identify the likelihood of each threat happening.
- Prioritise the threats.
Purpose of Risk Assessment
To prevent:
- Death and personal injury.
- Other types of loss incident.
- Breaches of statute law.
- The costs of loss.
A ‘Suitable and Sufficient’ Assessment
- Death Identify significant risks.
- Enable employer to identify and prioritise control measures.
- Appropriate to the nature of the work:
• Proportionate to the risks. - Valid for a reasonable time.
Group Exercise
- Sources of information can be:
• Internal to the organisation
• external to the organisation
List all the internal and external sources you can think of and discuss them.
Internal and External Information Sources
Internal:
- Accident records.
- Ill-health data/absence reports.
- Medical records.
- Risk assessments.
- Maintenance reports.
- Safety inspections.
- Audit and investigation reports.
- Safety committee minutes.
External:
- National legislation.
- Approved Codes of Practice.
- Standards e.g. BSI, ISO.
- Manufacturers’ information.
- Trade associations.
- Safety publications.
- International bodies.
- Trade unions, charities, etc.
Hazard Identification Methods
- Task analysis:
– Analyses job components before the job starts. - Legislation:
– Standards, guidance documents. - Manufacturers’ information:
– Operating handbooks, chemical safety data sheets. - Incident data:
– Accidents, near misses, ill health.
Hazard Identification Methods
Task analysis:
S – Select the task.
R – Record the stages of the task.
E – Evaluate risks associated with each stage.
D – Develop the safe working method.
I – Implement the safe working method.
M – Monitor to ensure effectiveness.
Step 2: Identify the People at Risk
- Workers/operators:
– Maintenance staff.
– Cleaners. - Contractors.
- Visitors.
- Members of the public – even trespassers.
Vulnerable groups or individuals:
- Young people.
- New or expectant mothers.
- Disabled workers.
- Lone workers.
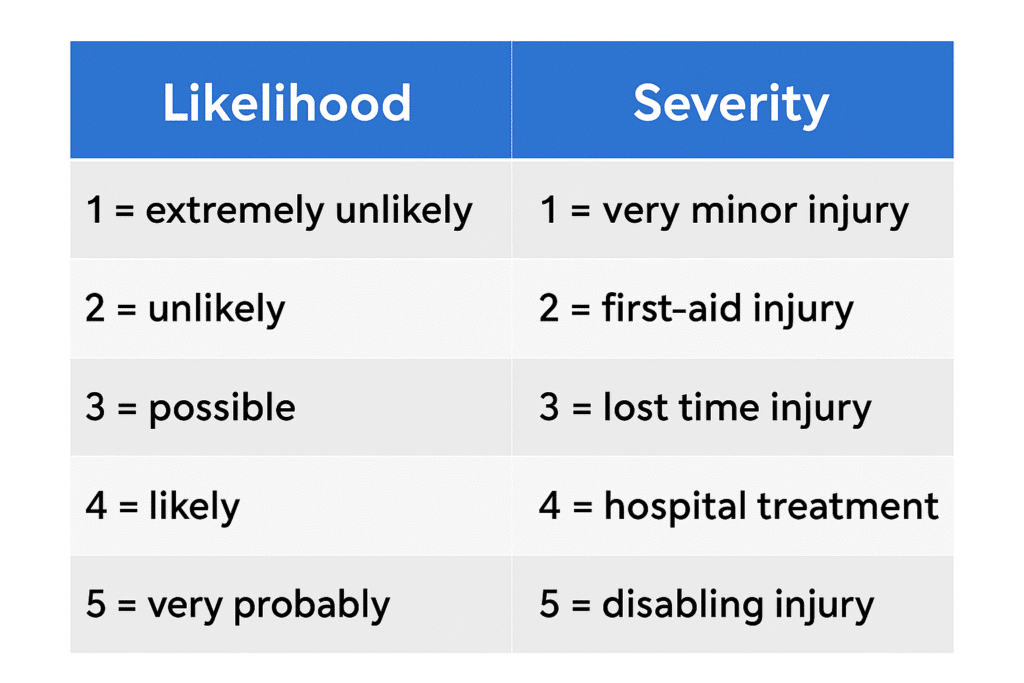
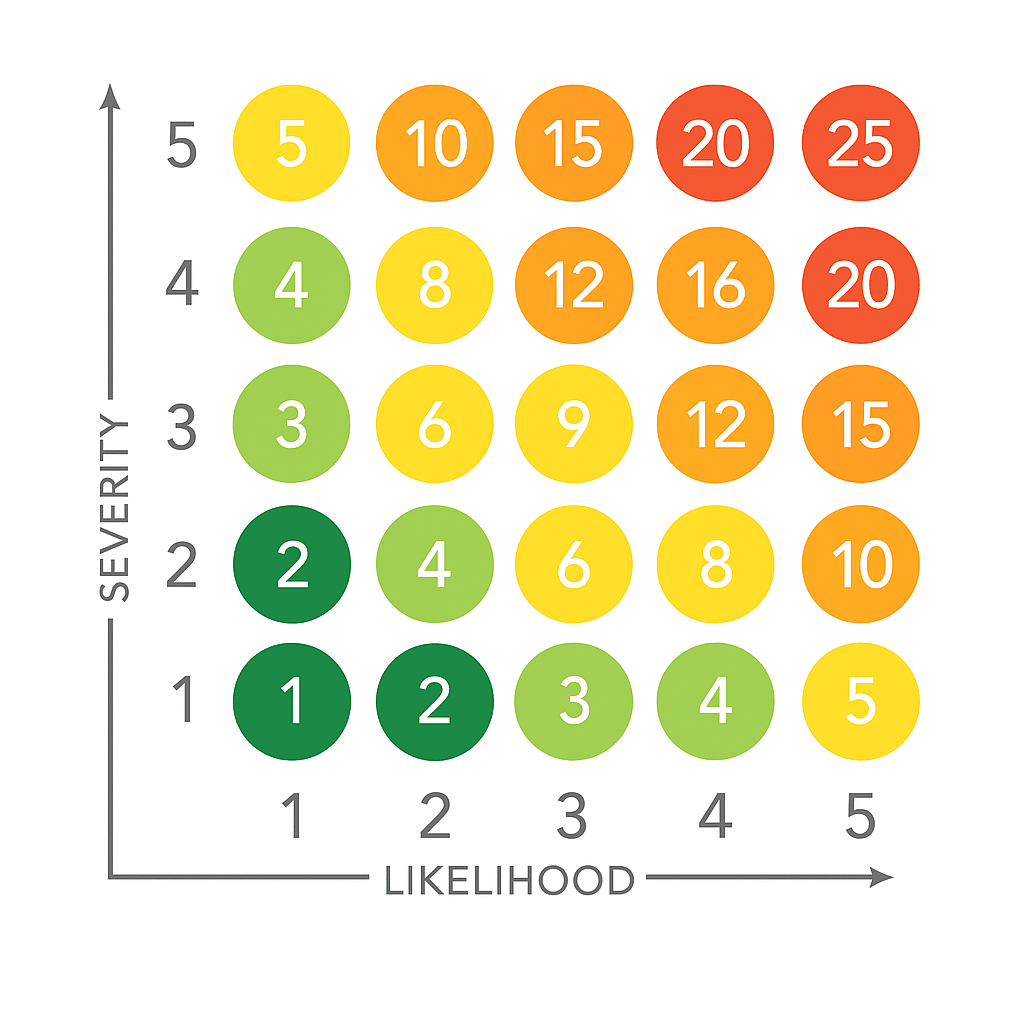
Step 3: Evaluating the Risk and Deciding on Precautions
Is the level of risk acceptable or does it need to be reduced?
Risk = likelihood × severity
General Hierarchy of Control
- Elimination.
- Substitution.
- Engineering controls.
- Administrative controls.
- PPE.
General Hierarchy of Control
- Elimination.
- Substitution.
- Engineering controls:
- Isolation, total enclosure.
- Separation, segregation.
- Partial enclosure.
- Safety devices.
- Administrative controls:
- Safe systems of work.
- Reduced exposure.
- Reduced time of exposure, dose.
- Information, instruction, training and supervision.
- PPE.
Safety Sign

Personal Protective Equipment (PPE)
Personal Protective Equipment Regulations 1992 (as amended)
- Supply suitable PPE:
• Appropriate for risk.
• Ergonomic.
• Fits.
• Doesn’t increase overall risk. - Complies with standards.
- Ensure compatibility of items.
- Suitable storage.
- Information, instruction and training.
- Enforce use of PPE.
- Replace or repair damaged or lost items.
Personal Protective Equipment (PPE)
| Merits | Limitations |
|---|---|
| 1. Can be used as an interim control whilst more expensive or difficult controls are put in place. | 1. It only protects one person – the wearer. |
| 2. In some situations, it may be the only control option available. | 2. It may not protect adequately if it is not fitted correctly. |
| 3. It may be needed as a back-up for emergencies when other controls have failed. | 3. It may not be comfortable and may interfere with the wearer’s ability to do the job. |
| 4. It is usually cheap. | 4. It may increase overall risk by impairing the senses (e.g. goggles that mist up). |
| 5. It gives immediate protection. | 5. It may not be compatible with other items that have to be worn or used. |
| 6. People do not like wearing PPE. | |
| 7. If it fails, it fails to danger (the worker is exposed to risk). |
Use of Guidance and Legal Standards
- Use of a risk matrix can help provide clarity:
– Can set internal risk levels that require action within set timescales. - Legal requirements override the findings of a risk assessment:
– Even if the risk is low, if the law requires it then it must be done.
– Applies also to semi-legal codes of practice.
– Guidance can also assist.
Residual, Acceptable and Tolerable Risk
- Residual Risk
– The risk level we are left with after controls have been implemented. - Acceptable Risk
– Risk has been reduced to an adequate level. - Tolerable Risk
– Not acceptable but can live with it for a short period of time with interim controls. - Unacceptable Risk
– Risk is too high.
Step 5: Review
NEBOSH-IGC
International General Certificate
Typical content:
- Activity/area assessed and hazards.
- Groups at risk.
- Risks and adequacy of existing control measures.
- Further precautions needed.
- Date and name of competent person.
- Review date.
- Significant change in:
– Process.
– Substances.
– Equipment.
– Workplace environment.
– Personnel. - If it is no longer valid:
– Accident.
– Near miss.
– Ill health.
– Change to legal standards. - Periodically.
Special Cases and Vulnerable Workers
Young Persons
- Under 18.
- Lack of experience.
- Physical and mental maturity.
- Poor risk perception.
- Influenced by peer group.
- Eager.
- Control measures:
– Prohibit certain high-risk activities, e.g. high-risk machinery.
– Restrict work patterns and hours, e.g. no overtime.
– Train and supervise.
Special Cases and Vulnerable Workers
New and Expectant Mothers
- Certain chemicals, e.g. lead.
- Certain biological agents, e.g. rubella virus.
- Manual handling.
- Temperature extremes.
- Whole-body vibration.
- Ionizing radiation.
- Night shifts.
- Stress.
- Violence.
Special Cases and Vulnerable Workers
Disabled Workers
- Identify, Health and fitness criteria for some jobs:
- E.g., eyesight requirements to drive forklift trucks.
- Workers with known disabilities:
- What are the implications of their disability?
Special Cases and Vulnerable Workers
Disabled Workers
- Identify, Health and fitness criteria for some jobs:
- E.g., eyesight requirements to drive forklift trucks.
- Workers with known disabilities:
- What are the implications of their disability?